Enterprises today are operating in an environment where complexity is outpacing traditional governance models. Studies show that most organizations now run close to 900 applications, yet less than a third are integrated, creating fragmented decision pathways and inconsistent oversight. Meanwhile, leadership priorities have shifted: nearly two-thirds of data leaders place governance above AI and analytics, recognising that automation, interoperability, and responsible intelligence all depend on a trusted foundation.
In our work with Fortune 500 firms across industries, we’re seeing this shift firsthand: manual processes are giving way to approaches that sync with how modern businesses actually work with embedded rules, consistent and scalable enforcement and verified information exchanges. This is where computational governance comes in: Automated and streamlined governance by embedding rules as executable, verifiable instructions inside the digital infrastructure, sometimes referred to as ‘Policies as Code’.
In this blog, we explore the drivers powering this shift, the technology pillars, use cases, and what’s next for embedding computational governance into modern enterprises.
Why Embedded Governance is Becoming the New Baseline
Across sectors, the conversation is moving from ‘How do we enforce governance?’ to ‘How do we compute governance into the fabric of the enterprise?’ This need for computational governance is driven by the realities of modern enterprises. Information exchanges now happen at a massive scale, between systems, people, industries, and the producers and consumers of data. Every interaction, whether a supplier updating inventory, a patient record moving across care providers, or a transaction in a financial system, creates an obligation to verify, to audit, to secure, to comply. Centralized governance efforts often operate differently from the way business units function day-to-day, creating gaps in oversight. In industries like financial services, healthcare, and consumer markets, this combination of scale, fragmentation, and regulatory pressure has made traditional governance insufficient.
Computational governance addresses these challenges by bringing automation into the way systems interact and rules are enforced. Instead of relying on multiple disconnected tools or documents, governance rules become executable within the infrastructure itself, enabling real-time enforcement and observability. This approach allows organizations to embed compliance directly into operational processes, monitor interactions across systems, and reduce the risk of process failures.
The targeted objectives of computational governance include:
- Ensuring compliance and risk mitigation: By embedding rules into systems, organizations can enforce policies automatically and maintain compliance at scale.
- Improving data quality and integrity: As information flows across different systems, computational governance ensures trust, transparency, and alignment with business outcomes.
- Optimizing resource utilization: Centralized policies can be effectively applied across federated business functions, leveraging shared standards while enabling individual teams to operate efficiently.
- Increasing transparency and accountability: Codifying processes and embedding governance into systems provides visibility and auditability, helping organizations demonstrate control and reliability to all stakeholders.
Thus, computational governance transforms governance from a manual, fragmented function into a continuous, reliable capability.
The Technology Pillars Enabling Computational Governance
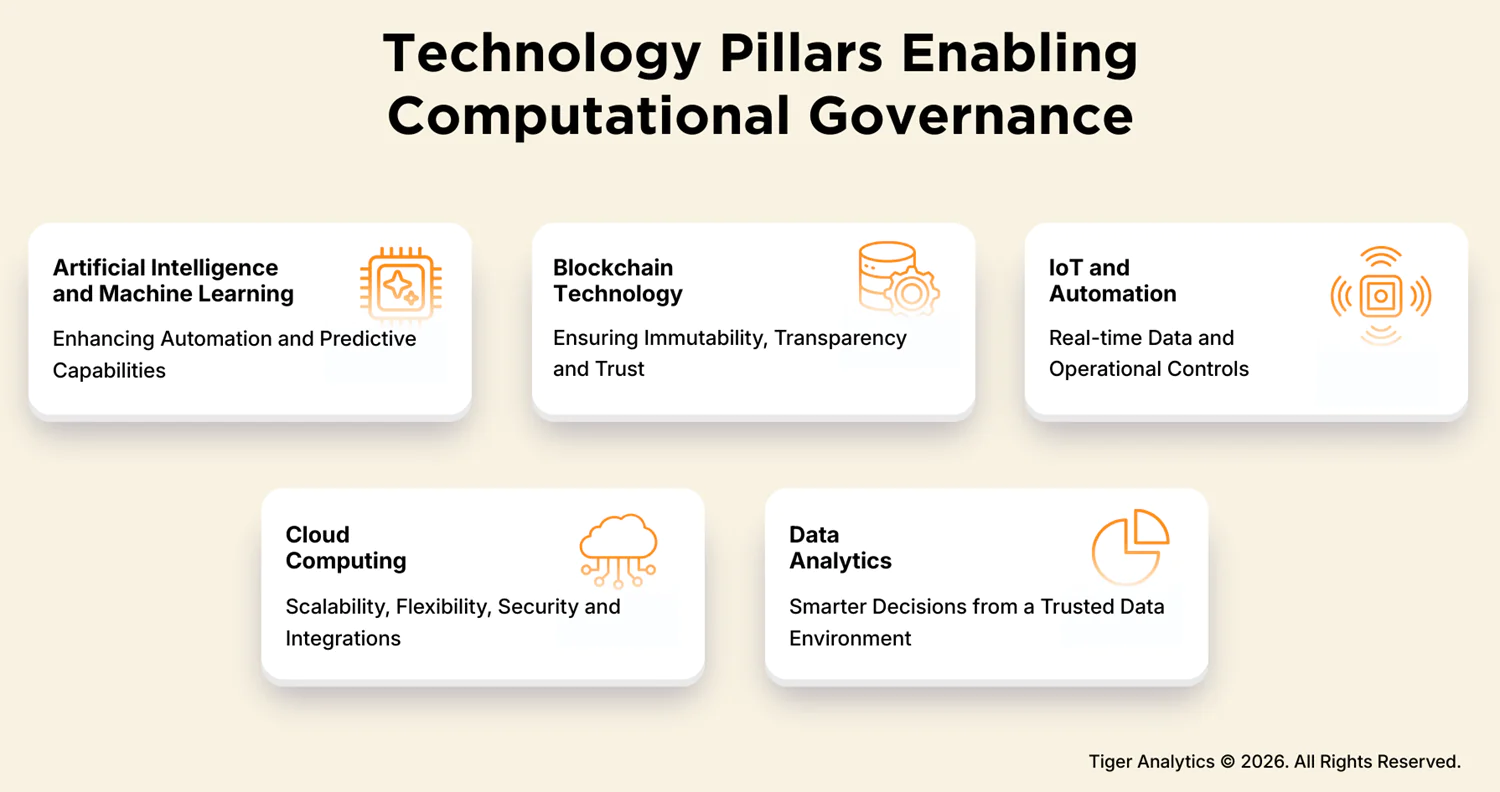
We view computational governance not as a single system or tool, but as the outcome of multiple technologies working together. Governance rules only have value when they can operate at the pace, scale, and complexity of modern enterprises, and that requires embedding intelligence, trust, real-time control, and analytical insight directly into operations. Our approach highlights five core pillars that make this possible:
1. Active Metadata & Data Graph
Moving from traditional static catalogs, in 2026 governance relies on Active Metadata, a continuous stream of telemetry from across the data stack.
- The shift: Instead of a human tagging a dataset as “Sensitive”, the system uses a Knowledge Graph to observe data movement and automatically apply labels based on lineage and usage patterns.
- Governance value: Provides the real-time context needed for “Policies-as-Code” to make intelligent decisions.
2. Agentic Policy Enforcement (Intent-Based Controls)
As organizations move from simple automation to Agentic AI, governance must evolve from simple ‘If/Then’ logic to intent-based networking and controls.
- The shift: Policies are no longer just access lists. Rather, they are guardrails that evaluate the intent of an AI agent’s request against corporate risk tolerance before execution.
- Governance value: Prevents autonomous drift, where AI agents might inadvertently violate compliance while trying to achieve a business goal.
3. Decentralized Identity & Verifiable Credentials (VCs)
The 2026 standard for interoperability is based on Self-Sovereign Identity (SSI).
- The shift: Rather than relying on a central database, systems use verifiable credentials to prove authority and compliance status instantly across organizational boundaries (e.g., in a Federated Data Mesh).
- Governance value: Eliminates the trust gap in partner ecosystems by allowing automated verification of security postures without manual audits.
4. Observability-Driven Compliance (ODC)
Governance is shifting from point-in-time audits to continuous observability.
- The shift: Tools now integrate Data Security Posture Management (DSPM) with real-time logs. If a configuration drifts from the Policy-as-Code definition, the system auto-remediates in milliseconds.
- Governance value: Turns audit trails into live dashboards, providing a real-time trust score for the entire enterprise.
5. Privacy-Enhancing Technologies (PETs)
With global regulations (like the EU AI Act) reaching full maturity in 2026, PETs are the standard for data sharing.
- The shift: Technologies like differential privacy, homomorphic encryption, and secure multi-party computation allow models to be trained and governed without ever exposing the underlying raw Personally Identifiable Information (PII).
- Governance value: Enables responsible intelligence by mathematically guaranteeing privacy, moving governance from a legal promise to a technical certainty.
These evolving trends are supported by the traditional pillars of Artificial Intelligence and Machine Learning that enhance automation and predictive capabilities; Blockchain Technology to ensure Immutability, transparency, and trust; IoT and Automation for real-time data and operational controls; Cloud Computing for scalability, flexibility, security, and integrations; and Data Analytics to enable smarter decisions from a trusted data environment. Together, these pillars form the backbone of our approach to computational governance.
Products Supporting Computational Governance
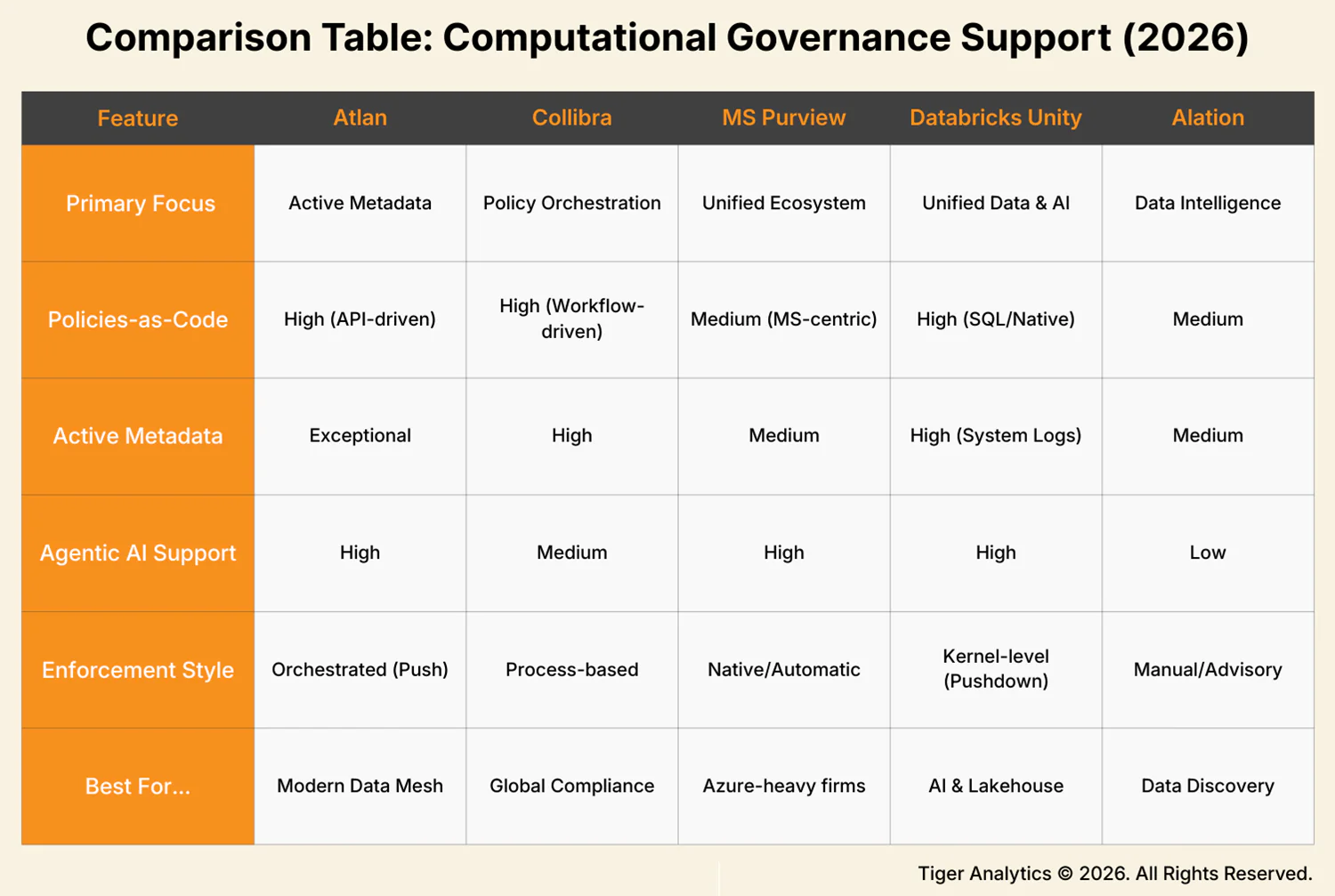
In 2026, the market for governance software has bifurcated. Traditional passive governance tools, which acted as digital libraries, are being rapidly replaced or augmented by active/computational Governance platforms.
Computational Governance in Practice: Success Stories from Real-world Deployments
Now that we’ve discussed the approach and technology, what does computational governance look like in reality? Here are three key cases that illustrate governance in motion: executable rules, real-time oversight, and automated compliance working seamlessly with operational processes, turning policies into practical, measurable outcomes.
SKU management and inventory optimization for an industrial organization: We worked with a leading global industrial company to harmonize item data across multiple ERPs and track product performance in real time. Governance embedded into operational systems enabled more accurate forecasting, optimized inventory, and reliable supply chain management. By integrating platforms with intelligent algorithms, data from production, logistics, and financial planning flowed seamlessly, supporting faster, more confident decisions on the shop floor and beyond.
Enhancing data trust and compliance for a healthcare provider: In the Medicare and Medicaid space, where rapid decisions affect patient care and regulatory outcomes, computational governance standardizes processes and automates oversight. In our work with a major healthcare provider, we integrated data quality management across business functions, improving traceability, enhancing trust scores, and minimizing compliance risk. Observability across patient encounters, pharmacy operations, and clinical workflows ensured predictable, auditable outcomes across complex data interactions.
Federated governance across global markets for a CPG firm: A global CPG company with multiple product lines and regional regulatory requirements partnered with us on a federated data mesh. With automated tool discovery, real-time monitoring of product quality, supply chain planning, and pricing operations, the firm could scale governance across markets. Embedding oversight into both internal and external data flows accelerated new data onboarding while maintaining consistency and transparency across the enterprise.
The Next Chapter: What We Must Solve and What We Stand to Gain
As computational governance becomes embedded across enterprise systems, new challenges emerge alongside the opportunities. One key area is algorithmic transparency and bias. Decisions increasingly rely on AI and machine learning models, making it essential to understand how models are trained, what assumptions are built in, and how governance is applied to ensure explainability and trust. Without this visibility, even automated governance can introduce unintended risks.
Other important caveats include privacy and data security. With data flowing across geographies, cloud platforms, and partner ecosystems, designing systems that safeguard sensitive information while enabling necessary data exchanges is a growing complexity. Similarly, systemic risk and unintended consequences can arise when large-scale processes and integrated systems operate at speed, making robust monitoring, auditability, and resilience critical.
At the same time, emerging technologies are expanding the possibilities. AI, machine learning, and generative AI capabilities can enhance computational governance by embedding intelligence and business- and role-aware context into decision-making. Cloud-native solutions and specialized platforms provide greater control over data sharing, security, and compliance, while custom solutions can tailor governance to unique enterprise needs.
Ethical governance is also gaining prominence. Cross-functional operating models, bringing together system owners, data stewards, business decision-makers, and developers, establish councils that guide the fair and responsible implementation of computational governance across the organization.
Looking ahead, the benefits are clear: faster, smarter, and more reliable decision-making; improved collaboration between centralized and federated functions; and higher accountability and transparency in both algorithms and governance processes. Computational governance is evolving from a framework into a dynamic, integrated capability that keeps pace with the complexity and speed of the digital enterprise.
References:
- https://www.precisely.com/blog/data-integrity/2025-planning-insights-the-rise-of-ai-is-hampered-by-a-lack-of-data-readiness
- https://www.mulesoft.com/lp/reports/connectivity-benchmark
- Gartner® Magic Quadrant™ for Data & Analytics Governance Platforms (2026) and Forrester Wave™ for Data Governance Solutions (2025)
- Collibra Platform Release Notes (February 20, 2026) and The 2026 Guide to Data Catalog Tools
- Gartner Peer Insights: Microsoft Purview Data Governance Reviews (2026) and Microsoft Inside Track (March 2026)
- Databricks Product Documentation (2026): Unity Catalog Attribute-Based Access Control (ABAC)
- Devoteam: AI & Agentic-ready Data Platforms Roadmap for 2026 and Hyperight: Top 12 Data Governance Predictions for 2026